Business IT Solutions Near Me: Why Proximity Is the Least Important Factor for Kansas City Firms
The "tech guy" down the street is likely the biggest threat to your compliance standing. Most Kansas City firm owners believe proximity equals responsiveness, but a quick response to a broken printer does not stop a HIPAA audit failure. When you search for business it solutions near me, you are usually met with generalists who treat security as an afterthought.
It is natural to want a partner who can be at your office in twenty minutes. You need to know that your workflows won't grind to a halt because of a hardware glitch. But for organizations that cannot afford to get this wrong, a fast drive time is a poor substitute for a rigorous compliance program.
This guide provides a strategic framework to help you prioritize security and regulatory evidence over mere physical location. You will learn how to vet an IT partner who takes the burden of SOC 2 or medical compliance off your plate entirely. We are moving past the myth of the local fix-it shop to find enterprise-grade protection that actually fits your budget.
Key Takeaways
- Learn why prioritizing proximity when searching for business it solutions near me often creates a dangerous "security-second" mindset for regulated firms.
- Categorize IT providers into three distinct tiers to understand why a standard MSP is no longer enough to protect organizations that cannot afford to get security wrong.
- Move beyond static compliance documents by implementing a program that generates the ongoing evidence required by HIPAA and SOC 2 regulations.
- Use our 5-point vetting framework to ask the uncomfortable questions that expose whether a vendor is a proactive shield or just a reactive repair service.
- Discover how to bridge the gap between enterprise-grade security and small business affordability without sacrificing the protection your industry demands.
The 'Near Me' Trap: Why Proximity Is a Liability for Regulated Kansas City Businesses
The local tech guy in Overland Park who drives to your office to swap out a router is a relic of 2005. For modern firms, relying on a local provider just because they're nearby is a dangerous gamble. This mentality focuses on physical presence while ignoring the digital perimeter where your actual risks live.
When searching for business it solutions near me, most Kansas City business owners prioritize speed of arrival. They want someone who can be in the office in twenty minutes. Reality dictates that by the time a technician pulls into your parking lot, your data is already gone.
To better understand this concept, watch this helpful video:
Effective IT is about a proactive shield, not a reactive repair service. We define this as Security-First IT Solutions. It's the difference between a fire alarm that calls the station and a sprinkler system that prevents the spark from ever catching. For Managed Security, the goal is total prevention.
Organizations That Cannot Afford to Get This Wrong understand that distance is irrelevant in a cloud-based world. They prioritize Managed services that offer 24/7 visibility over a local address. The search for business it solutions near me often leads to the wrong conclusion: that proximity equals protection. Most are not protected; they're just waiting for a local person to witness their downtime.
The Illusion of Local Support
Waiting for a technician to fight traffic on I-70 to reach Blue Springs is a failed strategy for 2026. Digital threats move at the speed of light. You don't need boots on the ground when you have eyes on the screen via Managed Detection and Response (MDR). Local reviews on generic platforms don't reflect technical competence in cybersecurity or the ability to manage complex compliance frameworks.
Why Proximity Doesn't Stop Ransomware
A breach in a Lee's Summit medical clinic happens in milliseconds. According to the IBM 2023 Cost of a Data Breach Report, it takes an average of 204 days just to identify a breach. Your provider's physical office in Lenexa won't stop an encryption script. What matters is the response time in the Security Operations Center (SOC). Under HIPAA Security Rule 45 CFR § 164.308(a)(1)(ii)(D), you must regularly review records of system activity. A local guy visiting once a month cannot meet this standard of continuous vigilance.
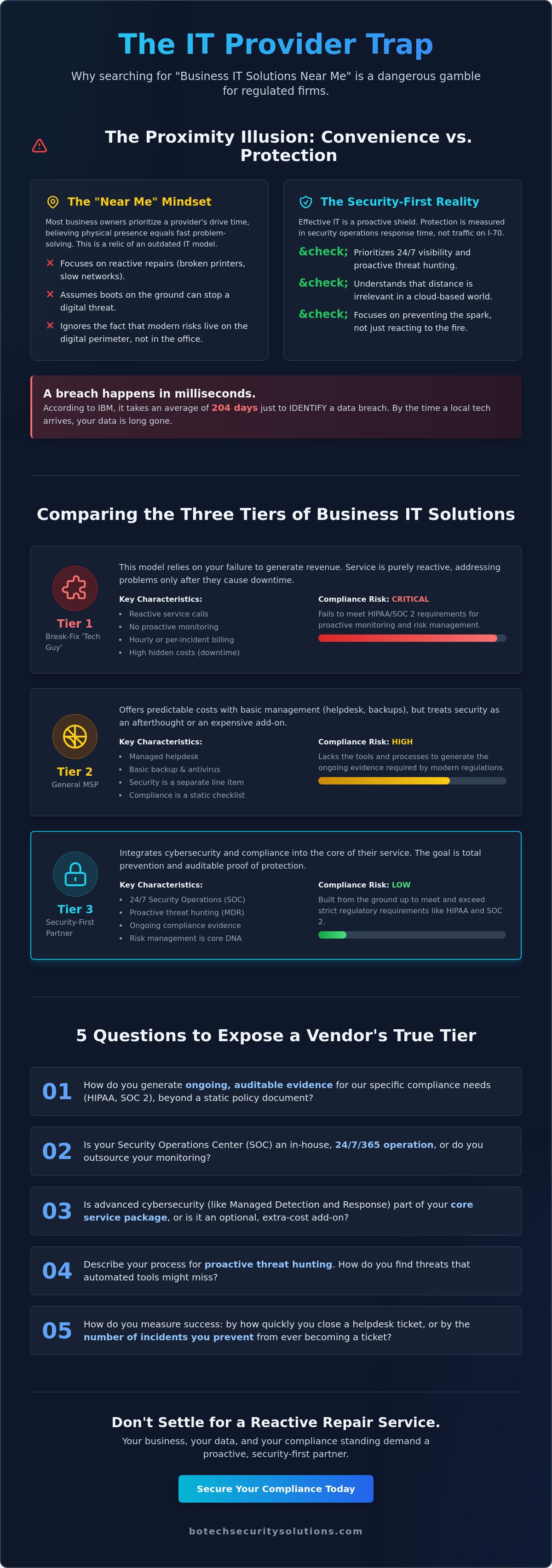
Comparing the Three Tiers of Business IT Solutions
Searching for business it solutions near me often leads to a dangerous assumption. Business owners in Tulsa, Oklahoma City, and Northwest Arkansas frequently believe that every IT provider offers the same baseline of protection. This is a myth that ends in data breaches and regulatory fines. Security isn't a sliding scale where you can be 70% protected. You are either secure or you are vulnerable. There is no middle ground when a ransomware group targets your firm's database.
Tier 1: The Break-Fix 'Tech Guy'
This model relies on failure to generate revenue. The provider only shows up when your server is down or your network is crawling. For a law firm in OKC or a clinic in NWA, this reactive approach is a death sentence for HIPAA or SOC 2 compliance. These regulations require proactive monitoring and risk management, not a guy who fixes things after they break. The hidden costs of unpatched vulnerabilities and hours of downtime far exceed any perceived savings. You can't ignore the Reality of HIPAA and SOC 2 requirements that demand constant vigilance. If your tech guy isn't looking for threats until you call him, you're already compromised.
Tier 2: The General Managed Service Provider (MSP)
Most providers fall into this category. They offer a helpdesk, basic backups, and a standard antivirus package. They are generalists who keep the lights on and the printers running. The uncomfortable truth is that most MSPs are not security experts. They might hand you a compliance document that looks official but lacks ongoing evidence of security controls. This is a trap for organizations that cannot afford to get this wrong. A PDF from three years ago won't satisfy an auditor when your patient records are leaked. You need a partner that understands the Managed Security landscape requires more than just a helpdesk ticket system. Many MSPs claim to do security, but they lack the 24/7 monitoring capabilities required to stop modern threats.
Tier 3: The Managed Security and Compliance Partner
This is the BoTech model designed specifically for regulated industries. We provide 24/7 Managed Detection and Response (MDR) and automated compliance tracking. We merge security with regulatory alignment because they are inseparable in today's legal environment. Our flat-rate model is the only way to align incentives between a provider and a client. We profit when you are secure and operational, not when you are struggling with tech issues. If you want to find out where you actually stand, you have to move beyond the generalist approach. This tier provides enterprise-grade protection at a price small businesses can actually afford. We don't just fix computers; we protect your reputation and your ability to practice law or medicine without fear of a compliance audit.
Compliance vs. Convenience: The Reality of HIPAA and SOC 2 in 2026
If you are a practice manager in Olathe or a legal partner in Fayetteville, searching for business it solutions near me often feels like the logical first step. You want someone who can walk through your front door when the server fails. This focus on physical proximity is a distraction from the high-stakes reality of modern regulation. Federal auditors do not care how close your IT provider lives to your office. They care about your data integrity and your ability to produce evidence of security at any given moment.
HIPAA Section 164.308(a)(1)(ii)(A) is very clear about the necessity of risk analysis. It is not a one-time event you complete to get a certificate for your lobby. It is a continuous requirement that demands constant vigilance. Organizations that cannot afford to get this wrong understand that safety is a daily discipline. Relying on a local "computer guy" who lacks a framework for continuous HIPAA compliance management is a liability you cannot justify to your board or your patients.
The Difference Between a Document and a Program
A compliance document is just a piece of paper. It tells a story about how your network looked on one specific Tuesday three months ago. A compliance program is an active engine that generates ongoing evidence. Most are not compliant even when they think they are because they treat SOC 2 or PCI DSS readiness as a yearly fire drill. They scramble to fix holes right before an audit and then let those same holes reopen once the auditor leaves.
Modern security requires automated evidence collection. This replaces the frantic search for logs and screenshots with a system that monitors your environment 24/7. It's the difference between a snapshot and a live video feed. If your current provider isn't providing a real-time dashboard of your compliance status, you are essentially flying blind between audit cycles.
Specific Regulatory Pressures in the KC Metro
Local enforcement trends for medical practices in Overland Park and Rogers show an increasing focus on technical safeguards. It's no longer enough to have a privacy policy in a binder. You must demonstrate active endpoint monitoring to satisfy federal law. Consider a small clinic in Broken Arrow that recently faced a "meaningful use" audit. They had the paperwork, but they couldn't prove that their encryption was active on every device during a specific six-month window.
This clinic faced significant penalties because their local IT provider focused on "fixing things" rather than "monitoring things." Proximity didn't save them from the audit. Only a structured program could have done that. You need a partner that treats your regulatory requirements as a technical constant rather than an occasional inconvenience.
- Continuous risk assessments replace the yearly panic.
- Automated logging satisfies HIPAA Section 164.308 requirements.
- Endpoint security provides the evidence trail needed for SOC 2.
The geography of your provider is irrelevant to the Department of Health and Human Services. What matters is their ability to manage your risk with enterprise-grade tools. You are either protected by a program or you are exposed by a document. There is no middle ground in 2026.
A 5-Point Framework for Vetting 'Business IT Solutions Near Me'
Searching for business it solutions near me usually feels like a quest for convenience. You want someone who can drive to your office in Bentonville or Springdale when a server goes dark. This is a legacy mindset that prioritizes physical presence over actual protection. A technician sitting in your lobby cannot stop a credential harvesting attack initiated from halfway across the globe. You need a partner who survives a rigorous interrogation before you grant them administrative access to your network.
Question 1: Do You Monitor My Network 24/7 or Just My Backups?
Many vendors claim they provide security when they are actually just managing backups. There is a massive difference between "it is backed up" and "it is being actively hunted for threats." A backup is a reactive tool used after a disaster has already occurred. Managed Detection and Response (MDR) is the digital equivalent of a 24/7 armed guard, not just a door lock. For legal firms in Tulsa, MDR is the baseline requirement to meet professional liability standards. If your provider isn't actively hunting for anomalies, they are simply waiting for you to fail.
Question 2: How Do You Generate Compliance Evidence Every Day?
Most small businesses rely on a "compliance document" that was written years ago and never updated. Real security requires a shift from thinking you are compliant to proving you are compliant. Ask your vendor about automated logging and real-time dashboarding for frameworks like HIPAA or SOC 2. You need to see the evidence of your security posture every day, not just during an audit. Our security-first support model focuses on creating a continuous stream of evidence that protects your reputation and your license.
Question 3: Is Your Own Staff Trained and Secure?
The uncomfortable truth is that many IT providers are the "patient zero" for supply chain attacks. If a hacker breaches your provider, they gain a back door into every one of that provider's clients. You must ask about their internal MFA protocols, their employee background checks, and their own security awareness training. Veteran-owned firms like BoTech prioritize operational security and discipline because we understand the stakes. We don't just secure your perimeter; we ensure our own internal house is a fortress that cannot be used against you.
Question 4: What is Your Guaranteed Response Time for Critical Security Events?
General IT support often prioritizes "first come, first served" tickets. A printer jam in Springdale should never take precedence over a suspected breach in your Kansas City headquarters. Ask for a specific Service Level Agreement (SLA) that differentiates between routine maintenance and security emergencies. You need a partner who treats a potential intrusion with the same urgency as a physical break-in.
Question 5: Can You Explain Your Stack Without Using Jargon?
If a vendor hides behind complex terminology, they are likely overcompensating for a lack of substance. A true partner can explain how they protect your data in plain English. They should be able to tell you exactly how they are stopping ransomware and how they are keeping you compliant with federal law. If they cannot explain the value of their business it solutions near me in simple terms, they don't understand the technology well enough to protect you.
Stop guessing about your security and start knowing exactly where your vulnerabilities are. Contact us today to find out where you actually stand.
Why BoTech Is the Strategic Ally for Kansas City Organizations
Searching for business it solutions near me often returns a list of local technicians who focus on fixing broken hardware. If you manage a healthcare practice in Blue Springs or a law firm in Lenexa, a local "computer guy" isn't enough. You belong to the group of organizations that cannot afford to get this wrong. A single data breach or a failed HIPAA audit can result in fines that exceed your annual profit. We built BoTech to bridge the gap between enterprise-grade security and small business budgets, ensuring that your location doesn't dictate your level of protection.
Our footprint spans from Bella Vista to Blue Springs, providing a regional dominance that understands the specific regulatory pressures of the Midwest. We don't just provide a compliance document that sits in a drawer. We implement a living compliance program that generates the ongoing evidence required by SOC 2 or PCI DSS standards. Proximity is a legacy metric; expertise and accountability are the modern standards for firms that value their reputation and their data.
Enterprise Security at a Small Business Price
We operate on a flat-rate model that eliminates the financial surprises common in the IT industry. Most vendors charge extra for incident response or vulnerability assessments when things go sideways. We include these critical services because security should never be a line-item negotiation. This "one partner" advantage is why financial firms in Oklahoma City and medical offices in Lenexa trust us to consolidate their security and compliance needs. It simplifies your overhead while hardening your defenses.
Our veteran-owned perspective drives a mission-first approach to every client relationship. We treat your digital perimeter with the same discipline required in high-stakes military environments. Most providers are reactive, waiting for your call to fix a problem that already happened. We are proactive guardians who identify vulnerabilities before they can be exploited by bad actors. You aren't just buying a service; you're gaining a strategic ally dedicated to your survival.
Next Steps: Finding Out Where You Actually Stand
Complacency is the primary reason small businesses remain vulnerable. You might think your current provider has everything under control, but most are not actually meeting modern security standards. We invite you to a free vulnerability assessment to see exactly what your "current guy" is missing. This isn't a high-pressure sales pitch. It is a diagnostic tool designed to give your leadership team the facts about your current risk profile.
You can also explore our Resources for additional tools to educate your staff on emerging threats. Understanding your gaps is the first step toward closing them. Don't wait for a ransom note to discover that your backups don't work or your encryption is outdated. Take control of your organization's security posture today.
Check your current admin passwords for MFA today. If your global administrator accounts do not require a second factor for login, your entire network is effectively unlocked for anyone with a stolen credential.
Moving Beyond Proximity to Proven Protection
You can't fix a HIPAA violation or a SOC 2 audit failure just because your IT provider is a ten-minute drive away. Modern security isn't about physical presence. It's about the technical depth required to defend against threats that don't care about Kansas City zip codes. Proximity is a comfort, but compliance is a requirement.
We've built a model specifically for organizations that cannot afford to get this wrong. As a veteran-owned and operated firm, we specialize in high-stakes frameworks like PCI DSS and include 24/7 Managed Detection and Response as a standard. When you search for business it solutions near me, remember that specialized expertise beats a local address every single time.
Your first step is simple. Review your current service level agreement today to see if 24/7 monitoring is a contractual guarantee or just a "best effort" promise. If the language is vague, your protection likely is too. You deserve a partner that takes your security as seriously as you take your business.
Ready to find out where you actually stand? Schedule your free security and compliance assessment today.
Frequently Asked Questions
Is it better to hire a local IT company in Kansas City or a national provider?
Expertise in your specific regulatory framework matters more than physical proximity. While many firms search for business it solutions near me, a partner's ability to implement enterprise-grade protection is the real priority. You need a firm that understands the binary nature of security, regardless of whether their office is five or five hundred miles away.
What is the average cost for managed IT solutions for a small business in Tulsa?
According to the 2023 Kaseya Global MSP Benchmark Report, small businesses typically pay between $100 and $250 per user per month for comprehensive managed services. Organizations that cannot afford to get this wrong should budget for the higher end of that spectrum. This investment ensures you receive proactive protection rather than reactive repairs that cost more in the long run.
Do I really need 24/7 monitoring if my office is only open from 9 to 5?
Yes, because the 2023 Verizon Data Breach Investigations Report indicates that 58 percent of cyberattacks target small businesses outside of standard business hours. Ransomware does not clock out at 5:00 PM. Continuous monitoring ensures that anomalies are detected and neutralized before your staff arrives the next morning, preventing a total operational shutdown.
Can an IT provider guarantee that I will pass a HIPAA audit?
No provider can legally guarantee you will pass a HIPAA audit. Any vendor making this claim is being dishonest about the nature of compliance. Your partner should provide a compliance program that generates ongoing evidence, but the ultimate responsibility for adherence to 45 CFR § 164.308 remains with the covered entity. We focus on building the evidence you need to prove your diligence.
What is the difference between a helpdesk and a Managed Security Service Provider (MSSP)?
A helpdesk fixes broken printers and resets passwords, while an MSSP focuses on threat detection and regulatory alignment. Most business it solutions near me offer basic support, but they lack the specialized security architecture required for regulated firms. You need one partner that can consolidate both your daily technical support and your high-level security needs into a single strategy.
How do I know if my current business IT solution is actually working?
You know your IT solution is working when you receive monthly reports showing successful patch deployments across 100 percent of your endpoints. If your only interaction with your provider is when something breaks, you have a reactive vendor rather than a proactive partner. Real protection is measured by the silence of a secure environment, backed by verifiable data that proves your systems are hardened.
Why should a law firm in Overland Park care about SOC 2 compliance?
Law firms in Overland Park handle sensitive client data that increasingly falls under the scrutiny of corporate clients requiring SOC 2 Type II reports. If you want to land contracts with enterprise-level organizations, you must prove your internal controls meet these rigorous standards. It's about more than just security; it's about business viability in a market where clients demand proof of protection.
What does 'flat-rate' IT support actually include?
A true flat-rate model includes unlimited remote support, proactive maintenance, and all necessary security software for a predictable monthly fee. It eliminates the conflict of interest found in hourly billing where the provider profits from your downtime. Most are not transparent about exclusions, so ensure your agreement covers both compliance services and core infrastructure management to avoid hidden costs.


