Cloud Integration Services in Kansas City: A 2026 Security and Compliance Reference
In September 2025, the Wyandot Center in Kansas City learned a hard lesson when a data breach affected 27,174 individuals through a single point of failure. You probably feel the pressure of managing fragmented data across multiple platforms while the threat of non-compliance fines looms over your office. Most vendors treat cloud integration services as a simple convenience for your workflow. We know it's actually a high-stakes expansion of your security perimeter that you cannot afford to get wrong.
It's frustrating to watch your data scatter across vendors while worrying if your security protocols actually talk to each other. You deserve a unified environment where protection works across every integrated platform automatically. This reference will teach you how to build a secure data flow that meets the strict standards of HIPAA and the 2026 Missouri Insurance Data Security Act. We'll explore how to generate ongoing compliance evidence so you stop relying on static documents that offer no real protection.
Key Takeaways
- Understand why cloud integration services act as a strategic expansion of your compliance perimeter rather than just a simple data sync.
- Identify the critical security gaps in native app connectors that often hide data sharing from office managers and compliance officers.
- Learn the specific steps to inventory your cloud connections and classify sensitive data like PHI and PII to prevent unauthorized access.
- Discover why maintaining encryption "in transit" between integrated nodes is non-negotiable for meeting 2026 Missouri insurance and healthcare regulations.
- Move beyond static compliance documents by implementing a system that generates the ongoing evidence needed to survive a SOC 2 or HIPAA audit.
The Cloud Integration Services Landscape in Kansas City: Beyond Simple Data Sync
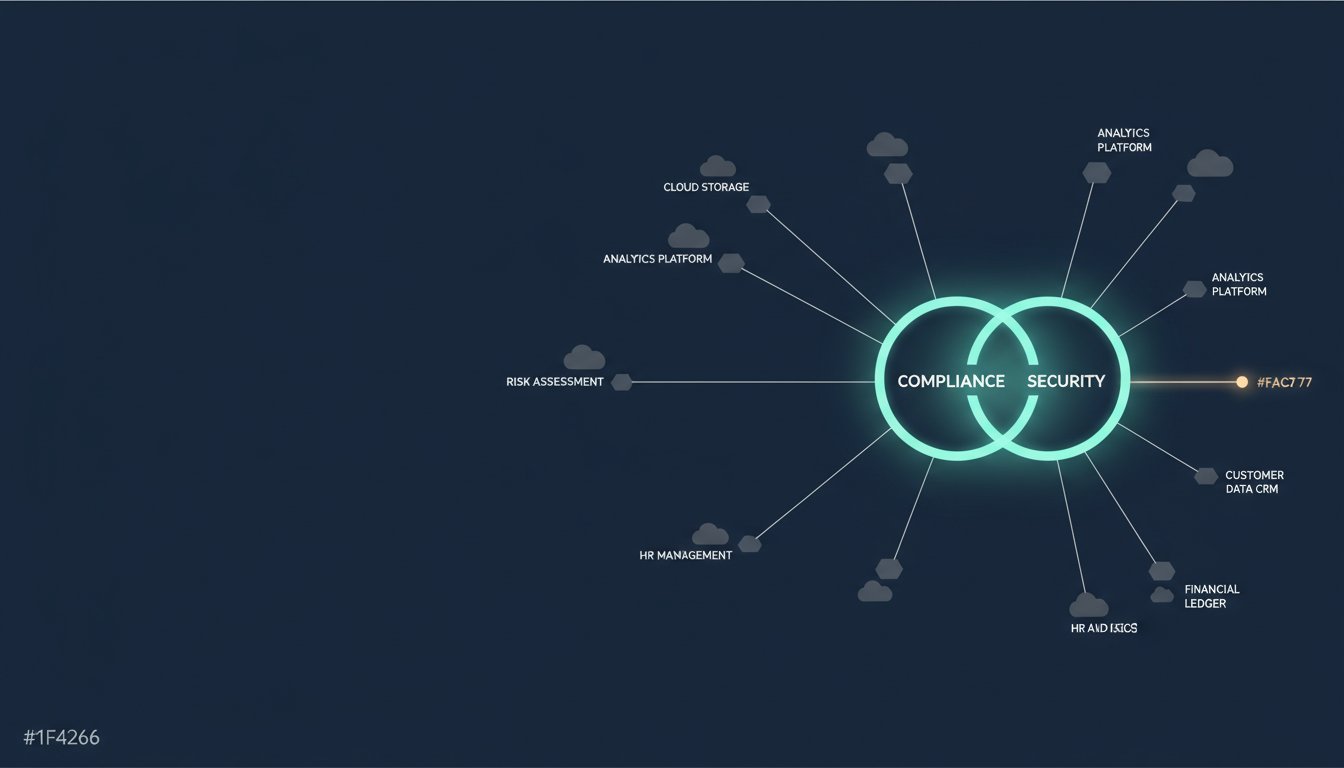
You might think connecting your CRM to your billing software is a simple task for your IT guy. In reality, cloud integration services represent the strategic architecture that keeps your disparate SaaS and on-prem systems from becoming a liability. For a healthcare practice in Overland Park, this isn't about convenience; it's about whether your patient data remains encrypted while it moves between platforms. Most office managers prioritize efficiency, but in the Kansas City metro, if your data moves, your compliance requirements follow it. You aren't just connecting apps; you're expanding your attack surface with every click.
To better understand how these systems communicate, watch this helpful video:
The Evolution of Integration in the KC Metro
Business owners in Lee’s Summit are moving away from the "all-in-one" platform myth because specialized software stacks simply perform better. Recent data indicates that 78% of organizations now utilize two or more cloud providers to manage their daily operations. This shift from manual entry to automated, API-driven workflows means your data is constantly in motion across the web. If that data includes Protected Health Information (PHI), your HIPAA obligations don't stop just because the data is currently between two different servers. The 2026 Kansas City Ordinance 251031 has already started shifting how local data centers operate, making it even more critical to know exactly where your integrated data lives and how it's being processed.
Why Integration is a Security Conversation, Not a Tech Feature
Here is the uncomfortable truth most vendors avoid: every integration point is a potential entry for a common cyber attack. Native connectors are often the weakest link in your security chain because they lack the granular visibility required for a legitimate audit trail. These connections frequently bypass traditional endpoint protection, creating a massive blind spot for your internal team. Under the Missouri Insurance Data Security Act (HB 974), effective January 1, 2026, you're required to conduct risk assessments that include these very integration points. You can't just "set it and forget it" when the law demands a written information security program that accounts for every path your data takes. Without active monitoring, a single compromised API key could expose your entire database before you even realize a connection was active. Check out our managed security to see how we monitor these integrated environments around the clock.
How Cloud Integration Services Work in Regulated Environments
For a busy practice manager, iPaaS sounds like just another technical acronym. Think of it as a digital traffic controller that ensures your data doesn't just move, but moves safely through a secure checkpoint. When you utilize cloud integration services, you're building a system that must adhere to strict federal guidance on cloud security to prevent unauthorized access during the "handshake" between two applications. Simple data syncing is a liability because it copies information from Point A to Point B without asking questions. Compliance-aware integration, however, logs every single transaction to create a trail that survives an audit.
Your data must remain encrypted "in transit" between these integrated nodes. If a Kansas City law firm connects its document management system to its billing platform, that connection cannot be a clear-text pipe. You also need centralized identity management, often through Single Sign-On (SSO), so your team has one set of keys to guard. This prevents the "password sprawl" that leads to 80% of data breaches according to the 2025 Verizon Data Breach Investigations Report. If you aren't sure how your current apps are talking to each other, you can reach out to us for a clear picture of your actual data flow.
HIPAA and SOC 2 Requirements for Cloud Data Flow
The HIPAA Security Rule, specifically Section 164.312(e)(1), requires you to implement technical security measures that guard against unauthorized access to PHI during transmission. A vendor might claim their app is "HIPAA compliant," but that doesn't mean the integration they built for you is secure. SOC 2 Trust Services Criteria also demand proof that your system remains protected and available. The uncomfortable truth is that most vendors provide a compliance document, which is just a piece of paper. A real compliance program generates ongoing evidence that your integration protocols are actually working as intended.
The Role of APIs in Legal and Financial Data Security
API keys are the literal "keys to the kingdom" for Kansas City legal firms. If these keys are hard-coded into a script or left unmanaged, an attacker can bypass your front door entirely. We've seen too many firms treat integration as a "set it and forget it" project, only to find unauthorized API calls months later. You need to monitor these calls for anomalous behavior, such as a sudden spike in data exports at 3:00 AM. This level of vigilance is a core part of a 24/7 managed security posture that protects your firm from the inside out.

Integration vs. Security: The Uncomfortable Truth About Native Connectors
Most office managers assume that if a software vendor provides a "native" button to connect to another app, the security is already handled. It isn't. This is the shared responsibility model in action where the vendor provides the pipe, but you remain responsible for every byte of data that flows through it. When you utilize cloud integration services, you aren't just linking tools; you're expanding your security perimeter into territory you likely don't control. Native connectors are built for marketing "seamlessness" rather than technical defense.
The uncomfortable truth is that these built-in tools are often the weakest link in your defense. Consider a Kansas City specialty clinic that integrated their CRM with an email marketing platform in late 2024 to automate patient follow-ups. The native connector requested "Full Admin" access to the database just to sync names and email addresses. Because no one was monitoring the actual data flow, a misconfiguration synced sensitive Protected Health Information (PHI) into a non-HIPAA compliant marketing cloud. This isn't a hypothetical risk; the Sunflower Medical Group breach in December 2024 impacted nearly 221,000 patients due to similar systemic vulnerabilities.
The Risk of "Shadow Integration"
Your employees are likely creating security gaps right now by using third-party automation tools to "save time" without any oversight. This "shadow integration" bypasses your traditional endpoint protection and creates hidden tunnels into your most sensitive legal or medical files. Most native connectors demand excessive permissions because it is easier for the developer, not because it is safer for your firm. You must audit your current integrations to find these "inadvertent actions" that could trigger a mandatory 45-day notification deadline under Missouri Rev. Stat. § 407.1500. Enterprise-grade protection requires a third-party layer of oversight that monitors these connections 24/7.
Compliance Program vs. Compliance Document
A signed Business Associate Agreement (BAA) is just a document; it does not stop a data leak or a misconfigured API. True cloud integration services require a compliance program that generates ongoing evidence of secure handling. We provide the independent verification that your software vendors simply won't offer. Relying on a vendor's word is a liability that the 96% of companies using cloud services cannot afford to take. We focus on integrated logging and active managed detection because that is the only evidence that holds up during a SOC 2 audit or a HIPAA investigation.
A Roadmap for Secure Cloud Integration Services in the KC Metro
Building a secure environment is not about buying more software; it's about disciplined execution. Most organizations treat their digital connections as invisible pipes that require no maintenance. This complacency is dangerous in a region where 96% of companies now rely on cloud services to some degree. You need a structured approach to ensure your cloud integration services don't become a backdoor for attackers. Follow these steps to secure your data flow today.
First, inventory every current cloud connection. You must document every bridge between your email, CRM, and accounting software. If you don't know a connection exists, you cannot secure it. Second, classify data sensitivity for every integration point. Identify where Protected Health Information (PHI) or Attorney-Client Privilege data resides. This allows you to apply the appropriate level of encryption and access control that meets your specific regulatory requirements.
Third, implement Multi-Factor Authentication (MFA) across all integrated platforms. MFA is your most effective defense against credential theft. If one app in your chain lacks this protection, the entire integration is compromised. Fourth, establish a centralized logging and monitoring system. You need to catch integration failures or unauthorized data exports in real-time. This provides the ongoing evidence required for a successful HIPAA or SOC 2 audit rather than just a static document.
Fifth, conduct a vulnerability assessment specifically targeting your cloud inter-dependencies. Standard scans often miss the gaps between applications. You need a focused look at how your platforms interact and where they might leak data. This level of scrutiny is what separates enterprise-grade protection from a standard small business setup.
Selecting the Right Integration Partner in Kansas City
Local support is critical when a data flow stops and your office grinds to a halt. You need a partner who understands the specific implications of the Missouri Insurance Data Security Act (HB 974) and local zoning ordinances like Ordinance 251031. The uncomfortable truth is that most local IT shops are helpdesks in disguise, lacking the security depth to manage complex cloud inter-dependencies. We bring a veteran-led discipline to managing digital infrastructures, ensuring your security is built-in rather than bolted on as an afterthought.
Immediate Actions for Regulated Small Businesses
You can improve your security posture today by performing a "least privilege" audit on your critical connectors. If an integration doesn't need "Full Admin" access to function, revoke those permissions immediately. Set up automated alerts for any new integration attempts in your Google or Microsoft environments to catch shadow integration early. For more context on building a secure foundation, read our guide on Managed IT Services for Small Businesses. If you want to see exactly where your connections stand, you can request a professional assessment of your current cloud environment.
Moving From Cloud Integration Documents to Evidence-Based Security
Kansas City organizations cannot afford to treat cloud integration as a one-time project. A signed contract or a compliance document is static; it doesn't watch your data at 2:00 AM. In 2025, the global average cost of a data breach hit $4.44 million according to IBM, with healthcare breaches soaring to $11 million. These numbers prove that relying on unmanaged cloud integration services is a gamble with your business's existence. We bridge the gap between high-end enterprise security and small business pricing through a flat-rate model that eliminates the hidden costs of insecure connections.
Security and compliance are not goals you reach; they are standards you maintain every single day. Most vendors will sell you a tool and walk away, leaving you to manage the complex inter-dependencies alone. We take a different approach by acting as a proactive partner that takes ownership of your safety. For Organizations That Cannot Afford to Get This Wrong, the distinction between implementation and management is the difference between a secure perimeter and a catastrophic leak.
The BoTech Approach to Cloud Security
Our 24/7 Managed Detection and Response (MDR) monitors your integrated environment for threats that traditional software misses. We act as the vigilant guardian of your perimeter, ensuring that every API call and data transfer adheres to the strict standards of HIPAA and SOC 2. By focusing specifically on the healthcare, legal, and financial sectors in the KC metro, we understand the specific regulatory pressures you face. You get the peace of mind of enterprise-grade protection without the enterprise-level overhead. Our managed services ensure that your security and compliance are active, ongoing processes rather than just checkboxes on a form.
Your Next Step Toward Secure Integration
Stop guessing about your actual security posture and start knowing. Most practice managers assume they are protected; most are not. Our assessment process is designed to show you exactly where you stand, identifying shadow integrations and excessive permissions before they become liabilities. You'll leave with a clear understanding of your data flow and a roadmap for genuine protection. Take the first step toward a secure, compliant future by choosing to find out where your organization actually stands today.
Your immediate action is to review your current vendor list and identify which third-party apps have "Admin" or "Write" access to your primary database. Once you've identified these connections, schedule your free security and compliance assessment to find out where you actually stand. This is your opportunity to move from the chaos of fragmented apps to the organized calm of a managed, secure environment.
Take Control of Your Data Perimeter
Your organization's safety depends on moving from passive trust to active verification. You've learned that native connectors often hide excessive permissions and that a signed BAA is no substitute for real-time monitoring. In the Kansas City metro, where tech jobs are projected to grow by 3,450 over the next decade according to local forecasts, the complexity of your digital stack will only increase. Relying on unmanaged cloud integration services is a risk that Organizations That Cannot Afford to Get This Wrong simply don't take.
We are a veteran-owned and operated partner specialized in the rigorous demands of HIPAA, PCI DSS, and SOC 2. Our 24/7 Managed Detection and Response ensures that your integrated environment remains a fortress rather than a sieve. You deserve the relief of knowing your enterprise-grade protection is handled by experts who understand the high stakes of Missouri and Kansas regulations. Don't let your data flow remain a mystery.
Your next step is simple and critical. Identify your single most important data connection and verify who has access to it today. Then, find out where your security actually stands with a Free Assessment. We'll help you transition from the anxiety of potential breaches to the confidence of a fully managed, secure environment.
Frequently Asked Questions
What are cloud integration services and why does my KC business need them?
Cloud integration services are the strategic architecture that connects your disparate software platforms into a unified, secure data flow. Your Kansas City business needs them because fragmented data creates security blind spots and operational bottlenecks that local regulations no longer tolerate. With 96% of companies now utilizing cloud services, you need a managed way to ensure these connections don't become unauthorized backdoors into your network.
Is cloud integration safe for HIPAA-regulated healthcare practices?
Integration is only safe when it includes technical safeguards like encryption in transit and centralized logging as required by HIPAA Security Rule 164.312(e)(1). Native connectors often fail this standard because they lack the granular audit trails needed to prove compliance during an investigation. Safe integration requires a managed layer that generates ongoing evidence rather than just a one-time setup.
How much do cloud integration services cost for a small law firm?
The cost of cloud integration services depends entirely on the complexity of your software stack and the level of ongoing management required to maintain security. While we don't provide fixed estimates without an assessment, the global iPaaS market is projected to reach $8.87 billion in 2026, reflecting the significant investment firms are making in secure connectivity. Investing in managed integration is always more affordable than the average $11 million cost of a healthcare data breach.
What is the difference between iPaaS and custom API integration?
iPaaS is a centralized platform that acts as a secure traffic controller for all your connections, while custom API integration is a direct, often unmanaged bridge between two specific apps. Custom APIs are risky because they frequently lack centralized logging and become "orphaned" when software updates occur. iPaaS provides the visibility and control that Organizations That Cannot Afford to Get This Wrong require for long-term stability.
Can cloud integration help my Kansas City business pass a SOC 2 audit?
Cloud integration helps you pass a SOC 2 audit only if the system is configured to provide continuous proof of the Trust Services Criteria. A document claiming your apps are connected is worthless to an auditor. You need a system that logs every transaction and monitors for anomalous behavior to provide the evidence-based security that auditors demand in 2026.
What happens if one of my integrated cloud services has a data breach?
You remain legally responsible for any patient or client data exposed through a third-party breach under Missouri Rev. Stat. § 407.1500. This law requires you to notify affected individuals within 45 days of discovery, regardless of which vendor "lost" the data. Managed cloud integration services provide the monitoring necessary to detect these breaches early and limit your liability through rapid incident response.
How do I know if my current cloud integrations are secure?
You don't know your integrations are secure unless you have performed a formal vulnerability assessment and a "least privilege" audit. Most office managers assume their connections are safe because they "just work," but this complacency is exactly what attackers exploit. If you cannot see a real-time log of every data transfer happening between your apps, your environment is likely vulnerable.
Do I need a local Kansas City provider for cloud integration management?
Local support is critical because you need a partner who understands state-specific mandates like the Missouri Insurance Data Security Act (HB 974). A local provider can offer rapid response when a critical data flow stops, ensuring your practice or firm doesn't grind to a halt. We provide the veteran-led discipline and regional expertise that national helpdesks simply cannot match.


