Why Your Kansas City IT Service Provider is Leaving You Exposed in 2026
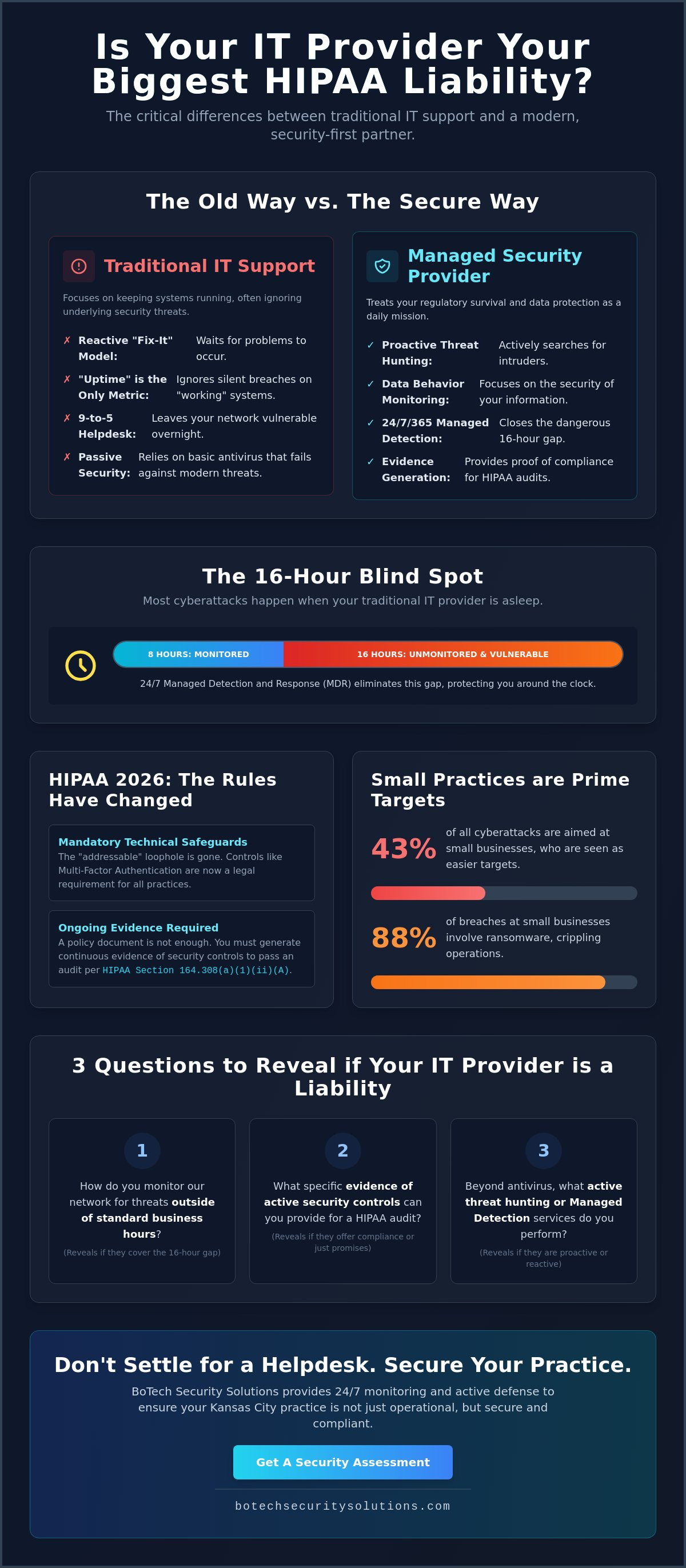
Your current IT provider is likely your biggest compliance liability. You pay them to keep your computers running, yet they often ignore the fact that the 2026 HIPAA Security Rule updates now make technical safeguards mandatory for every practice regardless of size. If they haven't already implemented multi-factor authentication across your entire network, they aren't just behind the curve. They're leaving you wide open.
You probably feel a sense of dread every time you hear about another local ransomware attack, like the one that recently crippled a neighboring organization's systems. It's frustrating to pay for support that ignores the root causes of your security anxiety. You deserve a managed security service provider kansas city, like BoTech Security Solutions, that treats your regulatory survival as a daily mission rather than a monthly invoice.
In this guide, you'll discover the dangerous myths of traditional IT and learn how to identify a security-first partner that actually protects your practice. We'll provide a clear framework to evaluate your current provider and explain what modern, 24/7 monitoring looks like. You'll leave with the confidence that your data is backed by ongoing evidence, not just a stack of empty promises.
Key Takeaways
- Learn why traditional "uptime" is a false metric that often hides active exploitations already living within your network.
- See why a security-first managed security service provider kansas city must monitor your systems 24/7 to close the dangerous 16-hour window left by standard IT support.
- Understand the critical distinction between simply owning a compliance document and generating the ongoing evidence required by HIPAA Section 164.308(a)(1)(ii)(A).
- Master three specific, non-confrontational questions that will immediately reveal if your current provider is a true security partner or just a reactive helpdesk.
The "Fix-It" Myth: Why Traditional IT Support Isnt Cybersecurity
Most Kansas City businesses treat their IT provider like a plumber. You call them when a pipe bursts or a printer stops spitting out invoices. This reactive model is a utility, but it isn't cybersecurity. There is a fundamental gap between a standard helpdesk and a true Managed Security Service Provider. While one focuses on keeping your staff productive, the other focuses on keeping your practice from being liquidated by a breach.
The uncomfortable truth is that your IT guy might be an expert at troubleshooting Windows updates while being completely invisible to a sophisticated intruder sitting on your network. In 2026, a "smoothly running" system is no longer a sign of safety. It's often a sign that an attacker is working quietly to avoid detection and maintain persistence.
To better understand this concept, watch this helpful video:
The Difference Between Maintenance and Defense
Patching a server is basic digital hygiene. It's the equivalent of locking your front door, but it doesn't stop someone who already has a key or knows how to pick the lock. A security-first managed security service provider kansas city doesn't just wait for a patch; they hunt for active threats. Traditional IT focuses on the health of the hardware, while a security partner focuses on the behavior of the data.
Traditional antivirus relies on a "set it and forget it" mentality that fails against modern ransomware. According to current industry data, 88% of small business breaches involve ransomware, a rate 2.3 times higher than at larger organizations. Effective incident response requires an urgency and specialized skillset that a 9-to-5 helpdesk simply cannot provide. We look for the threats that bypass standard filters, because relying on a passive shield is a recipe for disaster.
Why "Everything is Working" is a Dangerous Metric
Modern breaches often occur without a single minute of system downtime. Attackers prefer your systems to stay "up" so they can slowly exfiltrate protected health information (PHI) without triggering alarms or panic. If your only metric for IT success is that the lights are on and the internet is fast, you are flying blind. You might be "working" your way right into a catastrophic data loss event.
Small businesses are now the primary target, accounting for 43% of all cyberattacks. 24/7 vigilance is the only acceptable standard because hackers don't take the weekend off. By May 2026, the updated HIPAA Security Rule eliminates the "addressable" loophole, making specific technical controls a legal requirement for your practice. If you can't produce evidence of these controls during an audit, your "working" systems won't save you from significant federal penalties.
24/7 Managed Detection vs. Periodic Network Maintenance
Managed Detection and Response (MDR) is the functional difference between a smoke detector and a full-time fire department. While traditional IT support might check your server health once a month, an MDR service monitors every digital heartbeat in real-time. For an office manager at a Kansas City clinic, this means knowing that a suspicious login attempt at midnight is being handled while you are at home.
The uncomfortable truth that most vendors avoid is that their "24/7 support" often just means an answering service that takes a message until morning. This leaves a 16-hour window every day where your network is essentially unmonitored. Attackers know your staff is home and your IT provider is asleep, making the overnight hours the prime time for data exfiltration.
The IBM Cost of a Data Breach Report 2025 highlights that organizations with high levels of security automation and professional monitoring identified breaches 100 days faster than those without. Speed is the only metric that matters when your reputation is on the line. A managed security service provider kansas city focuses on shrinking that detection window from months down to minutes.
The Role of Continuous Threat Hunting
Imagine a workstation in your law firm begins communicating with a known malicious server at 2:00 AM. An automated antivirus might block a specific file, but a human-led security analysis determines if the intruder is already moving through your folders. We don't just wait for the alarm to ring; we investigate the shadow behind it.
Our team actively hunts for these anomalies to isolate infected devices before they can compromise your entire network. This proactive stance is a core component of modern HIPAA Security Rule guidance, which emphasizes the need for ongoing risk management. You can speak with a specialist to see how this level of vigilance fits your specific practice requirements.
Endpoint Protection Beyond the Office Walls
In 2026, your office is wherever your laptop or smartphone happens to be. Traditional maintenance often fails to account for the vulnerability of a partner working from a coffee shop or a nurse accessing records via a tablet at home. We treat every device as a high-stakes gateway that must be secured with the same rigor as your main server.
Protecting attorney-client privilege and patient privacy requires more than just a simple password. It requires advanced endpoint protection that travels with the data, ensuring that sensitive information remains encrypted and monitored regardless of the network connection. This level of oversight ensures that your firm remains compliant with professional standards and Missouri or Kansas privacy laws.
The Compliance Document Trap: Why Policies Wont Stop a HIPAA Audit
Many practice managers sleep soundly because they have a thick 3-ring binder labeled "HIPAA Policies" on their shelf. This is a dangerous delusion. A policy is just a promise to behave a certain way, but an auditor from the Office for Civil Rights (OCR) doesn't care about your promises. They want proof that you actually did what you said you would do.
The uncomfortable truth is that a binder of paper is useless during a live security incident or a federal audit. You need a managed security service provider kansas city that focuses on generating ongoing evidence rather than just static documentation. If you can't produce a log showing who accessed a specific record at 3:00 AM last Tuesday, your policy binder is just expensive wallpaper.
HIPAA Section 164.308(a)(1)(ii)(A) specifically mandates that covered entities conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information. In 2026, a "thorough assessment" isn't a one-time event. It requires the continuous collection of technical data that proves your safeguards are active and effective at all times.
Generating Ongoing Evidence for SOC 2 and PCI DSS
SOC 2 readiness is a state of being, not a one-off project you "complete" to get a certificate. You don't "prep" for an audit in the modern regulatory environment; you remain in a state of continuous audit readiness. This transition requires moving away from manual checklists and toward automated systems that capture technical evidence in real-time. An effective IT partner ensures that your security controls are always generating the telemetry needed to satisfy an auditor's request without disrupting your daily operations.
The Reality of HIPAA Fines in 2026
By May 2026, the U.S. Department of Health and Human Services (HHS) has finalized updates that eliminate the flexibility of "addressable" safeguards. Technical controls like Multi-Factor Authentication (MFA) and encryption are now mandatory for every organization, regardless of size. Failing to implement these and provide evidence of 24/7 monitoring often lands a practice in the "Willful Neglect" category of fines. This classification carries much higher financial penalties and more frequent oversight. You can explore our Kansas City HIPAA Compliance Solution to see how managed security provides the evidence you need to stay on the right side of the law.
Auditing Your Current IT Service Provider: Three Questions That Reveal the Truth
You probably like your current IT person. They're friendly, they fix the Wi-Fi, and they've been with you for years. However, professional likability is not a security control. In 2026, the technical requirements for healthcare and legal practices have moved far beyond basic troubleshooting and printer repairs.
You don't need a computer science degree to figure out if you're actually protected. You just need to ask the right questions and listen for specific, evidence-based answers. If your provider reacts with vagueness or defensive corporate jargon, you have your answer. A high-level managed security service provider kansas city will welcome these questions because their systems are designed to provide this transparency every day.
Question 1: Who is watching our endpoints at 3 AM on a Sunday?
If the answer is "the software," you're exposed. Software is a passive tool that can be bypassed or silenced by a sophisticated attacker. You need to know if a human being in a 24/7 Security Operations Center (SOC) is actually reviewing alerts when your office is closed. This distinction is vital because most ransomware attacks are launched during off-hours to maximize the time an intruder has to move through your network. You can learn more about why this proactive approach is mandatory in our guide to Managed IT Support Services in Kansas City.
Question 2: Can you show me the evidence of our compliance from last Tuesday?
This is a "show, don't tell" moment. A provider who says "we're doing it" is giving you a promise, not a program. Ask them to pull the logs or technical evidence for a specific, random date in the past. In 2026, real-time visibility is the only acceptable standard for regulated businesses. If they have to spend three days "preparing a report" to show you basic security telemetry, they aren't actually monitoring your network in a way that would satisfy an auditor.
Question 3: What was the result of our last simulated phishing campaign?
Cybersecurity is not just a technical problem; it's a human one. Industry data shows that 95% of cybersecurity incidents are attributed to human error. If your provider isn't regularly testing your staff with simulated phishing attacks, they're ignoring the most common point of failure. You should be able to see which employees clicked a link and what specific training they received as a result. This is a critical defense against the Common Cyber Attacks Targeting Kansas City Businesses.
If these questions make your current provider uncomfortable, it's time to find out where you actually stand with a professional security assessment.
Beyond the Helpdesk: Securing Your Kansas City Practice with BoTech
BoTech Security Solutions exists to solve the high-stakes problem of technical accountability for regulated businesses. Most small organizations in the Kansas City area are caught between two bad options. They either face expensive enterprise security firms that don't want their business or local helpdesks that don't understand how to generate regulatory evidence. We act as the bridge, providing high-level protection and compliance management at a scale that makes sense for a growing law firm or medical practice.
As a veteran-owned managed security service provider kansas city, we don't do fluff or marketing jargon. We operate with a no-nonsense approach to technical protection that prioritizes the integrity of your data above all else. Our model is built on a flat monthly rate that includes 24/7 Managed Detection and Response. This ensures your costs remain predictable while your security remains absolute.
The BoTech Security Solutions Difference: Vigilance as a Service
We replace the distant, reactive vendor relationship with a proactive partnership. Instead of waiting for you to report a problem, we take ownership of your security posture by consolidating IT support, security, and compliance into a single point of contact. This is especially critical for the healthcare, legal, and financial sectors where a single audit failure can result in catastrophic financial penalties.
Our focus is on generating the ongoing evidence required by standards like SOC 2 and the 2026 HIPAA updates. We don't just give you a document; we give you the technical proof that your organization is actually safe. This transition allows you to move from a state of constant anxiety over local ransomware attacks to a state of controlled, compliant calm. You can explore our full range of security resources to see how we maintain this standard.
Your Next Step: The Free Security Assessment
The first step toward real protection is a truth-finding mission. Our free security assessment is not a high-pressure sales pitch. It is a technical deep dive designed to show you exactly where your current vulnerabilities live and how they map against current regulations. We provide the hard truths that most vendors prefer to avoid.
You will receive a clear understanding of your current risks without the sugar-coating common in the IT industry. This assessment provides the framework you need to evaluate your current provider and make informed decisions about your organization's future. It is time to stop guessing about your safety and start knowing exactly where you stand.
Before you do anything else, ask your current IT person to provide a report of all successful logins to your network from outside the United States over the last 30 days. If they cannot produce this evidence within ten minutes, you have a visibility gap that an attacker is already waiting to exploit. Find out where you actually stand with a free assessment and take control of your practice's security today.
Take Control of Your Regulatory Future
You now have the framework to distinguish between a reactive helpdesk and a true security partner. Traditional IT support focuses on keeping your computers running, but a security-first managed security service provider kansas city focuses on keeping your practice in business. Real safety requires the continuous generation of technical evidence and 24/7 monitoring that never sleeps. A binder of policies on a shelf is not a compliance program; it's a liability waiting for an auditor to find it.
BoTech has been veteran-owned and operated since 2021. We specialize in navigating the complex technical requirements of HIPAA, SOC 2, and PCI DSS for organizations that cannot afford the cost of a breach. Our service model includes 24/7 Managed Detection and Response because we refuse to leave your data unmonitored for 16 hours a day. We provide the high-level protection your practice needs with the direct, human accountability you deserve.
The path from vulnerability to confidence starts with a single honest look at your current network. You deserve a partner that takes ownership of your protection so you can focus on your patients and clients. Find out where you actually stand with a free security assessment. We are ready to help you secure your future.
Frequently Asked Questions
What is the difference between an MSP and an MSSP?
An MSP focuses on making sure your technology works, while a managed security service provider kansas city focuses on making sure your technology is safe. Standard providers handle things like email setup and printer connectivity. We handle the technical safeguards that protect your data from exfiltration and ensure you meet federal requirements. This distinction is critical because uptime doesn't equal security.
Does my small Kansas City business really need 24/7 security monitoring?
You need 24/7 monitoring because cybercriminals launch most attacks during off-hours to maximize their dwell time before being noticed. Leaving your network unmonitored for 16 hours a day is an unacceptable risk for any regulated practice. The city of Wichita learned this the hard way when a ransomware attack forced a total IT shutdown in May 2024. Proactive monitoring is the only way to stop an intrusion before it becomes a headline.
How much does a managed security service provider typically cost?
Pricing for managed security services is typically structured as a predictable monthly investment based on the number of users or devices in your organization. This model covers the cost of the 24/7 security operations center and the specialized software agents required for endpoint protection. It replaces the unpredictable costs of emergency repairs with a stable budget for continuous defense. You pay for the stability of a secure environment rather than the chaos of a recovery.
Will a new IT service provider replace my existing hardware?
Most security implementations don't require you to replace your existing computers or servers immediately. We typically layer specialized security agents and monitoring tools onto your current infrastructure to provide immediate protection. If a specific piece of hardware is too old to support modern technical safeguards like encryption or multi-factor authentication, we'll tell you exactly why it's a liability. We prioritize protecting what you have while planning for necessary upgrades.
How long does it take to get a law firm compliant with SOC 2?
Achieving SOC 2 readiness is a continuous process that usually takes several months to establish a valid evidence trail. It isn't a one-time project you can rush through with a simple checklist. You must demonstrate that your security controls have been active and effective over a period of time to satisfy an auditor's requirements. We help you build the systems that generate this evidence automatically, moving you from audit preparation to a state of constant readiness.
Can an IT service provider help me lower my cyber insurance premiums?
Implementing robust security controls like Multi-Factor Authentication and 24/7 monitoring is often a prerequisite for qualifying for a cyber insurance policy in 2026. Insurance carriers now demand proof of active threat hunting and formal incident response plans. By reducing your risk profile through professional oversight, you make your organization a better candidate for lower premiums. You aren't just buying security; you're buying a more defensible business profile.
What happens if we have a security incident while under your care?
We isolate the infected device immediately to prevent the threat from spreading across your entire network. Our 24/7 team detects the anomaly and begins remediation the moment an alert is triggered. We also provide the technical evidence needed for mandatory reporting, ensuring you meet the 72-hour restoration requirements found in the updated HIPAA Security Rule. This rapid response minimizes downtime and protects your reputation during the most critical moments of an incident.


